Introduction
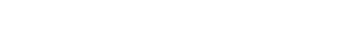
Consider a group of users (Alice and Bob) who want to share documents among themselves while keeping them secret from adversaries (one of which is Eve) who have complete access to the system on which the documents were shared (think of a Google Doc that Google can not read). By leveraging cryptographic protocols and primitives such as Public Key Encryption, Hashing, and Message Authentication Codes to protect the identities of the users and protect the integrity of the documents – the sharing system and the documents shared can be kept secret from unauthorized users.
The first problem to be solved is in sharing the documents
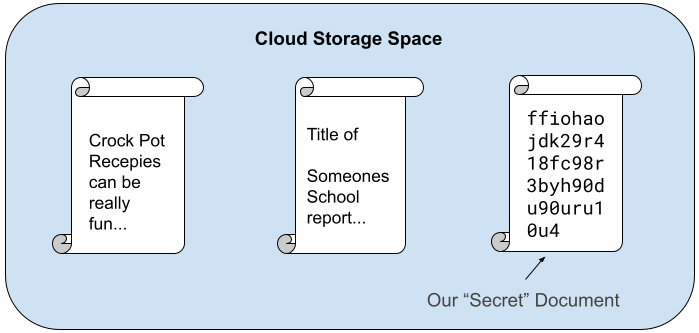
If Alice shares a document with Bob, Eve is allowed to intercept that share. Eve can also modify it. Bob must be able to detect any tampering done to the shared document prior to reading it. Also if Eve intercepts the share, she should obtain no information about the location of the document within the system. This means that file metadata (such as the date, title, and author) should be encrypted and only visible to Bob. When Bob receives the share, Bob now has the location of the document, the name of the document, and the privilege to share this document with others. This creates a tree-like sharing structure where Alice is allowed to revoke privilege to Bob which in turn revokes privilege to anyone with whom Bob shared the document.
A system to revoke privilege to documents is in place to keep previously trusted users and the users with whom they shared the documents from reading any additions to the documents unless they are authorized. By leveraging a combination of cryptographic primitives, Alice can revoke access to a document shared with Bob. Even if Bob shared the document with Kayla and Max, the newly appended information can’t be read by either Bob, Kayla or Max while leaving the sharing structure intact for other privileged users like Michael to read and write to the document.
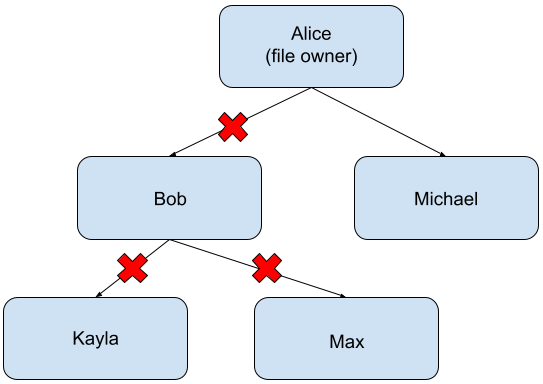
What about editing shared documents?
To add flexibility to the system, appending to files has been implemented without overwriting previously written data. This decreases the amount of work necessary to append to documents, keeps the on-disk files holding the documents with many additions small, and hides the size of files from adversaries. Cryptographic primitives like Message Authentication Codes and Public Key Encryption were leveraged to maintain the confidentiality and integrity of all pieces of the documents for all privileged users.
Project details
Unfortunately I am unable to publicly post implementation details or link to a repository. This project was implemented in GoLang and I would be happy to discuss specific details over a coffee. Please reach out if you want to learn more.